KAUST Information Security Department
Credit Card Fraud – January 2018 Phishing Campaign: Winners and Information
Each simulation results in a prize draw to reward our vigilant users who are the fastest to report a phishing email. We rely on our users to be aware of phishing threats and report emails to us that may bypass our controls. We are pleased to announce that this month’s winners are:
- Khalid Mostafa
- Kathleen Hoffman
- Christopher Joseph

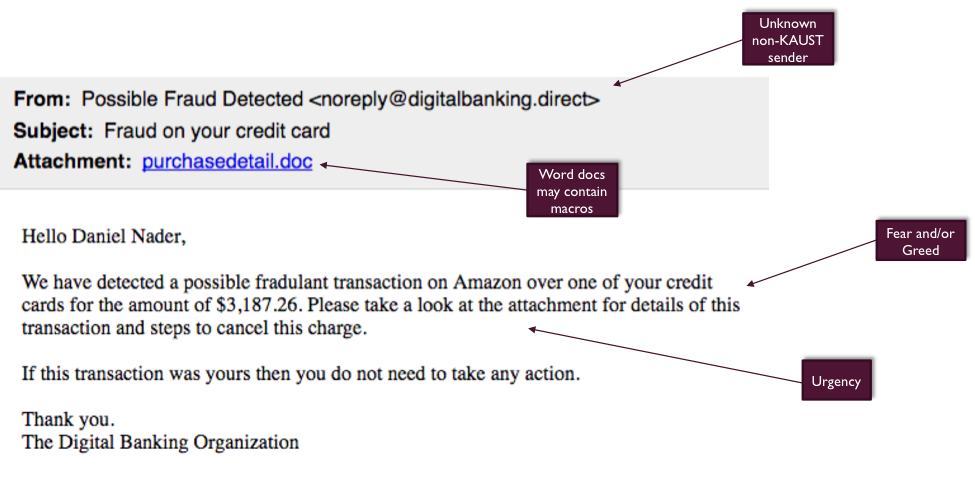
Figure 1: Results of our most recent phishing campaign run from 21 January through 23 January 2018.
- It was sent from a generic sender – “Possible Fraud Detected”. If you checked the email address, it is was not a KAUST email, but rather noreply@digitalbanking.direct
- The signature is “The Digital Banking Organization” – this is text which can type into an email
- The email has typos and improper punctuation which signals lack of legitimacy
- The email preys on the user’s emotions, their sense of duty and fear of being charged for fradulent activity
See below for a breakdown:
Questions?
PHISHING F.A.Q:
Q- What is phishing?
A- Sending emails purporting to be from familiar sources in order to build trust and induce individuals to reveal personal information, such as passwords or credit card numbers. This can also apply to chat messages or SMS.
Q- What is KAUST doing about phishing?
A- We do have technical controls and response teams that are working around the clock, those cover the majority of harmful behaviors programmed into malicious codes. However, hackers with the intent of causing harm are always trying to stay one step ahead by evading these controls with what appears to be a harmless email. It then becomes the job of the user to be vigilant and identify such emails.
The KAUST Information Security Department will from time to time conduct phishing simulations by sending out similar emails to train individuals on identifying such emails and stay vigilant and aware. The scope of these simulations is everyone with a KAUST account.
Q- How do I react when I suspect an email to be a phishing attempt?
A- Report it! Whether it is a real phish from a hacker, a simulation by Information Security, or an email that just does not feel right; you should always report it. This has immensely helped us in the past in thwarting off hacking attempts.
Any user using Microsoft Outlook on Mac or Windows will have a ‘Report a Phish’ button. In the event you do not use Microsoft Outlook, you can forward the email to phishreporter@kaust.edu.sa.
Windows Users: The button is found in the ribbon on the top right of the screen. Highlight the email you want to report and then click the button.
Mac Users: The button is found in the dock on the bottom left of the screen (This can be customized by users). Highlight the email you want to report and then click the button.
If you do not see the button or cannot find it; contact the IT HelpDesk and they can assist you.
Q- Sometimes I see announcements (like this one) that have links leading to sites other than KAUST’s, what should I do?
A- KAUST Announcements and Lens Posts use a system called E2MA, links will direct to the tool first for statistical purposes and then take you to the content you want to see. Wufoo, Form Stack, and Survey Monkey are some of the other tools used for surveys and online forms and can all be considered safe. Our best advice is to always check the sender and if in doubt, contact the sender or report it to us for analysis.
Q- How is phishing different from spam?
A- Spam is the annoying and sometimes meaningless email junk that comes into our inboxes. It does not ask for your personal or confidential information and is frequently advertisements sent in bulk to many users. Phishing on the other hand asks you to click on a link, provide your username/password, banking information, or sensitive information. Spear-phishing is when it becomes a targeted email sent to a specific user or set of users.

